CyberAlerts is shutting down on June 30th, 2025. Thank you for your support!
Example Searches:
CVE
Threat Actors
Countries
Vendors
Severity
Known Exploited
|
CVE-2025-29627 |
Description: An issue in KeeperChat IOS Application v.5.8.8 allows a physically proximate attacker to escalate privileges via the Biometric Authentication Module
CVSS: MEDIUM (6.8) EPSS Score: 0.03%
June 9th, 2025 (4 days ago)
|
|
CVE-2024-47081 |
Description: Requests is a HTTP library. Due to a URL parsing issue, Requests releases prior to 2.32.4 may leak .netrc credentials to third parties for specific maliciously-crafted URLs. Users should upgrade to version 2.32.4 to receive a fix. For older versions of Requests, use of the .netrc file can be disabled with `trust_env=False` on one's Requests Session.
CVSS: MEDIUM (5.3) EPSS Score: 0.06%
June 9th, 2025 (4 days ago)
|
|
CVE-2024-0542 |
Description: A vulnerability was found in Tenda W9 1.0.0.7(4456). It has been rated as critical. Affected by this issue is the function formWifiMacFilterGet of the component httpd. The manipulation of the argument index leads to stack-based buffer overflow. The attack may be launched remotely. The exploit has been disclosed to the public and may be used. The identifier of this vulnerability is VDB-250712. NOTE: The vendor was contacted early about this disclosure but did not respond in any way. Eine kritische Schwachstelle wurde in Tenda W9 1.0.0.7(4456) ausgemacht. Dies betrifft die Funktion formWifiMacFilterGet der Komponente httpd. Dank der Manipulation des Arguments index mit unbekannten Daten kann eine stack-based buffer overflow-Schwachstelle ausgenutzt werden. Der Angriff kann über das Netzwerk passieren. Der Exploit steht zur öffentlichen Verfügung.
CVSS: HIGH (8.8) EPSS Score: 0.14% SSVC Exploitation: none
June 9th, 2025 (4 days ago)
|

|
Description: SentinelOne has shared more details on an attempted supply chain attack by Chinese hackers through an IT services and logistics firm that manages hardware logistics for the cybersecurity firm. [...]
June 9th, 2025 (4 days ago)
|
|
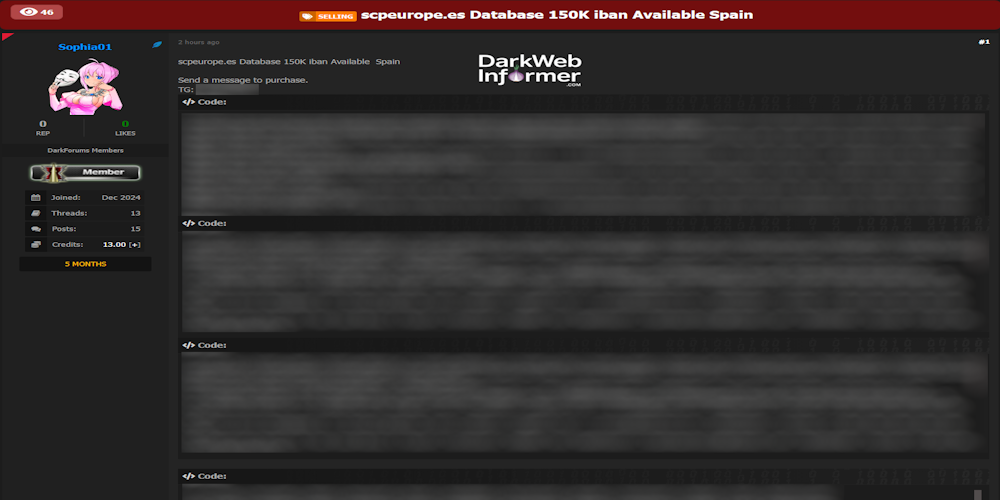
Description: Alleged database sale SCP Spain
June 9th, 2025 (4 days ago)
|

|
Description: A collective of former WordPress developers and contributors backed by the Linux Foundation has launched the FAIR Package Manager, a new and independent distribution system for trusted WordPress plugins and themes. [...]
June 9th, 2025 (4 days ago)
|

|
Description: Summary
The application does not sufficiently sanitize user input, allowing for the execution of arbitrary JavaScript code. The 'saveNode' and 'saveManifest' endpoints take user input and store it in the JSON schema for the site. This content is then rendered in the generated HAX site.
Although the application does not allow users to supply a 'script' tag, it does allow the use of other HTML tags to run JavaScript.
Affected Resources
Operations.php:258 saveManifest()
Operations.php:868 saveNode()
https:////system/api/saveNode
https:////system/api/saveManifest
Impact
An authenticated attacker can use the site editor and settings editor to store malicious payloads in a HAX site which execute arbitrary JavaScript when a user visits the site. This can be used to steal a user's session cookie or other sensitive data.
PoCs
saveNode
To replicate this vulnerability, an attacker can use the "View Source" functionality within the site editor to enter a malicious payload.
Select "View Source" within the HAX site editor and enter an XSS payload that does not use the "script" HTML tag.
Select "Update HTML" and observe the resulting alert.
saveManifest
To exploit the 'SaveManifest' endpoint, an attacker can insert executable code into the URL field of the site settings editor: any payload added this way will execute when the site is loaded.
Open the site settings editor.
Add JavaScript code to the URL field under the "Theme" header.
Reload the page to run the script.
...
June 9th, 2025 (4 days ago)
|

|
Description: Summary
An authenticated Local File Inclusion (LFI) vulnerability in the HAXCMS saveOutline endpoint allows a low-privileged user to read arbitrary files on the server by manipulating the location field written into site.json. This enables attackers to exfiltrate sensitive system files such as /etc/passwd, application secrets, or configuration files accessible to the web server (www-data).
Details
The vulnerability stems from the way the HAXCMS backend handles the location field in the site's outline. When a user sends a POST request to /system/api/saveOutline, the backend stores the provided location value directly into the site.json file associated with the site, without validating or sanitizing the input.
Later the location parameter is interpreted by the CMS like in HAXCMSSite.php line 1248 to resolve and load the content for a given node. If the location field contains a relative path like ../../../etc/passwd, the application will attempt to read and render that file.
PoC
Authenticate to the CMS and retrieve the JWT and CSRF token.
Issue a POST request to /system/api/saveOutline with the path traversal injection via the location parameter :
Curl the website root to see the file contents.
Impact
This is an authenticated Local File Inclusion (LFI) vulnerability, via the location parameter the attacker can read any file on the filesystem that is accessible by the www-data user.
References
https://github.com/haxtheweb/issues/security/advisories/GHSA-hxrr-x32w-cg...
June 9th, 2025 (4 days ago)
|
|
CVE-2025-32433 |
🚨 Marked as known exploited on June 9th, 2025 (4 days ago).
Description:
CISA has added two new vulnerabilities to its Known Exploited Vulnerabilities (KEV) Catalog, based on evidence of active exploitation.
CVE-2025-32433 Erlang Erlang/OTP SSH Server Missing Authentication for Critical Function Vulnerability
CVE-2024-42009 RoundCube Webmail Cross-Site Scripting Vulnerability
These types of vulnerabilities are frequent attack vectors for malicious cyber actors and pose significant risks to the federal enterprise.
Binding Operational Directive (BOD) 22-01: Reducing the Significant Risk of Known Exploited Vulnerabilities established the KEV Catalog as a living list of known Common Vulnerabilities and Exposures (CVEs) that carry significant risk to the federal enterprise. BOD 22-01 requires Federal Civilian Executive Branch (FCEB) agencies to remediate identified vulnerabilities by the due date to protect FCEB networks against active threats. See the BOD 22-01 Fact Sheet for more information.
Although BOD 22-01 only applies to FCEB agencies, CISA strongly urges all organizations to reduce their exposure to cyberattacks by prioritizing timely remediation of KEV Catalog vulnerabilities as part of their vulnerability management practice. CISA will continue to add vulnerabilities to the catalog that meet the specified criteria.
CVSS: CRITICAL (10.0)
June 9th, 2025 (4 days ago)
|

|
Description: A security researcher has revealed a technique for brute-forcing the full phone numbers linked to Google accounts using a now-deprecated JavaScript-disabled username recovery form. The proof-of-concept attack exploited lax rate-limiting and token validation mechanisms to systematically identify phone numbers tied to specific display names. The issue was first investigated by the researcher in early 2025 …
The post Google Flaw Allowed Brute-Forcing Users’ Phone Numbers appeared first on CyberInsider.
June 9th, 2025 (4 days ago)
|
