Example Searches:
CVE
Threat Actors
Countries
Vendors
Severity
Known Exploited

|
Description: This vulnerability allows remote attackers to create a denial-of-service condition on affected installations of Linux Kernel. Authentication is not required to exploit this vulnerability, but only systems with ksmbd enabled are vulnerable. The ZDI has assigned a CVSS rating of 6.8.
May 29th, 2025 (12 days ago)
|
|
CVE-2025-46701 |
Description: Improper Handling of Case Sensitivity vulnerability in Apache Tomcat's GCI servlet allows security constraint bypass of security constraints that apply to the pathInfo component of a URI mapped to the CGI servlet.
This issue affects Apache Tomcat: from 11.0.0-M1 through 11.0.6, from 10.1.0-M1 through 10.1.40, from 9.0.0.M1 through 9.0.104.
Users are recommended to upgrade to version 11.0.7, 10.1.41 or 9.0.105, which fixes the issue.
EPSS Score: 0.02%
May 29th, 2025 (12 days ago)
|

|
Description: Red Canary's MDR portfolio complements Zscaler's purchase last year of Israeli startup Avalor, which automates collection, curation, and enrichment of security data.
May 29th, 2025 (12 days ago)
|

|
Description: [AI generated] USMortgage.com is a financial service provider located in the United States, specializing in home mortgages. The company offers a variety of loan products, including conventional, FHA, VA, USDA, and jumbo mortgages. It seeks to harmonize technology with customer service to streamline home financing and refinancing processes for borrowers. USMortgage.com prides itself on transparency, education, and personalized customer support.
May 29th, 2025 (12 days ago)
|

|
Description: In addition to Coca-Cola, entities in Abu Dhabi, Jordan, Namibia, South Africa, and Switzerland are experiencing extortion attacks, all involving stolen SAP SuccessFactor data.
May 29th, 2025 (12 days ago)
|
|
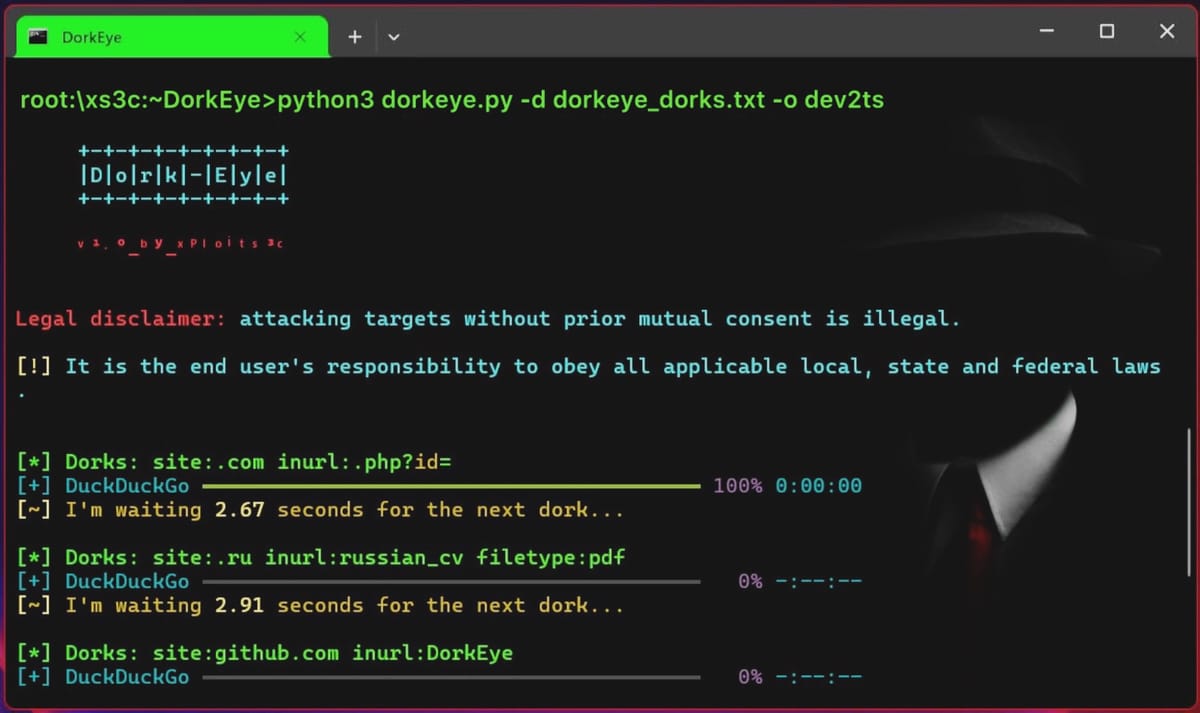
Description: DorkEye: A Python Script for Ethical Dorking
May 29th, 2025 (12 days ago)
|
|
May 29th, 2025 (12 days ago)
|

|
Description: IT management software firm ConnectWise says a suspected state-sponsored cyberattack breached its environment and impacted a limited number of ScreenConnect customers. [...]
May 29th, 2025 (12 days ago)
|

|
Description: The company said it “recently learned of suspicious activity” within its environment that it believes “was tied to a sophisticated nation state actor, which affected a very small number of ScreenConnect customers.”
May 29th, 2025 (12 days ago)
|

|
Description: Talos Content Manager Amy introduces themself, shares her unconventional journey into cybersecurity and reports on threats masquerading as AI installers.
May 29th, 2025 (12 days ago)
|
