Example Searches:
CVE
Threat Actors
Countries
Vendors
Severity
Known Exploited

|
Description: DaVita Inc falls victim to INTERLOCK Ransomware
April 24th, 2025 (8 days ago)
|

|
Description: One of the ways threat actors keep up with the constantly evolving cyber defense landscape is by raising the level of sophistication of their attacks. This trend can be seen across many of our engagements, particularly when responding to China-nexus groups. These actors have demonstrated the ability to create custom malware ecosystems, identify and use zero-day vulnerabilities in security and other appliances, leverage proxy networks akin to botnets, target edge devices and platforms that traditionally lack endpoint detection and response, and employ custom obfuscators in their malware. They take these extra steps to evade detection, stifle analysis, and ultimately stay on systems for longer periods of time.
However, not all successful attacks are highly complex and technical. Many times attackers will take advantage of the opportunities that are made available to them. This includes using credentials stolen in infostealer operations to gain initial access. Mandiant has seen such a rise in infostealer use that stolen credentials are now the second highest initial infection vector, making up 16% of our investigations. Other ways attackers are taking advantage of opportunities is by exploiting gaps and risks introduced in cloud migrations, and targeting unsecured data repositories to obtain credentials and other sensitive information.
Today we released M-Trends 2025, the 16th edition of our annual report, to help organizations stay ahead of all types of attacks. We dive de...
April 24th, 2025 (8 days ago)
|
|
April 24th, 2025 (8 days ago)
|
|
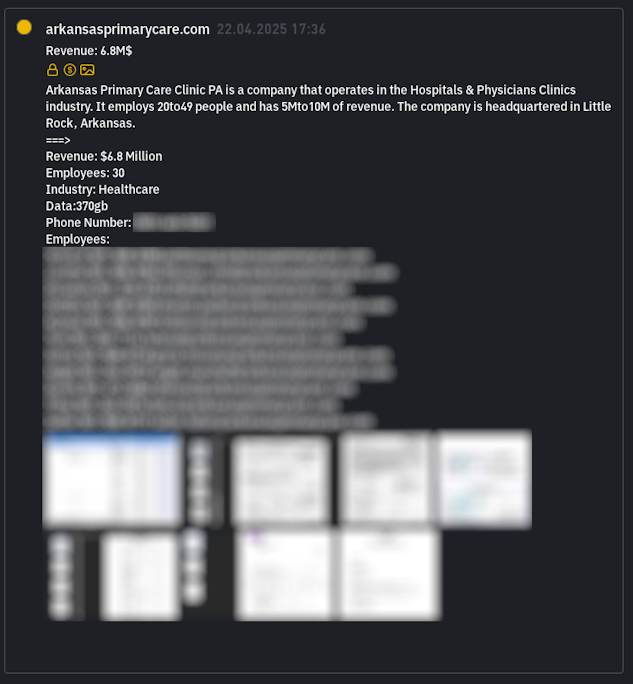
Description: Arkansas Primary Care Clinic has Fallen Victim to INC RANSOM Ransomware
April 24th, 2025 (8 days ago)
|

|
Description: Dress To is a women's clothing brand.
We are going to to upload more than 34 GB of essential corporate
documents such as: employees and customers personal files (identi
ty cars, passports and so on), financial data (audits, payment de
tails, reports), corporate agreements, etc.
April 24th, 2025 (8 days ago)
|

|
Description: Impact
A leniency in h11's parsing of line terminators in chunked-coding message bodies can lead to request smuggling vulnerabilities under certain conditions.
Details
HTTP/1.1 Chunked-Encoding bodies are formatted as a sequence of "chunks", each of which consists of:
chunk length
\r\n
length bytes of content
\r\n
In versions of h11 up to 0.14.0, h11 instead parsed them as:
chunk length
\r\n
length bytes of content
any two bytes
i.e. it did not validate that the trailing \r\n bytes were correct, and if you put 2 bytes of garbage there it would be accepted, instead of correctly rejecting the body as malformed.
By itself this is harmless. However, suppose you have a proxy or reverse-proxy that tries to analyze HTTP requests, and your proxy has a different bug in parsing Chunked-Encoding, acting as if the format is:
chunk length
\r\n
length bytes of content
more bytes of content, as many as it takes until you find a \r\n
For example, pound had this bug -- it can happen if an implementer uses a generic "read until end of line" helper to consumes the trailing \r\n.
In this case, h11 and your proxy may both accept the same stream of bytes, but interpret them differently. For example, consider the following HTTP request(s) (assume all line breaks are \r\n):
GET /one HTTP/1.1
Host: localhost
Transfer-Encoding: chunked
5
AAAAAXX2
45
0
GET /two HTTP/1.1
Host: localhost
Transfer-Encoding: chunked
0
Here h11 will interpret it as two requests, one with body AAAAA45 and one wi...
April 24th, 2025 (8 days ago)
|

|
Description: Drowning in security data but missing real threats? Learn how threat actors exploit this paradox—and how to turn your data into actionable intelligence.
April 24th, 2025 (8 days ago)
|

|
Description: Summary
After some research, it turns out that it is possible to force an application to switch to SPA mode by adding a header to the request. If the application uses SSR and is forced to switch to SPA, this causes an error that completely corrupts the page. If a cache system is in place, this allows the response containing the error to be cached, resulting in a cache poisoning that strongly impacts the availability of the application.
Details
The vulnerable header is X-React-Router-SPA-Mode; adding it to a request sent to a page/endpoint using a loader throws an error. Here is the vulnerable code :
To use the header, React-router must be used in Framework mode, and for the attack to be possible the target page must use a loader.
Steps to reproduce
Versions used for our PoC:
"@react-router/node": "^7.5.0",
"@react-router/serve": "^7.5.0",
"react": "^19.0.0"
"react-dom": "^19.0.0"
"react-router": "^7.5.0"
Install React-Router with its default configuration in Framework mode (https://reactrouter.com/start/framework/installation)
Add a simple page using a loader (example: routes/ssr)
Send a request to the endpoint using the loader (/ssr in our case) adding the following header:
X-React-Router-SPA-Mode: yes
Notice the difference between a request with and without the header;
Normal request
With the header
Impact
If a system cache is in place, it is possible to poison the response by completely altering its content (by an error message), strongly impacting its ava...
April 24th, 2025 (8 days ago)
|

|
Description: Summary
After some research, it turns out that it's possible to modify pre-rendered data by adding a header to the request. This allows to completely spoof its contents and modify all the values of the data object passed to the HTML. Latest versions are impacted.
Details
The vulnerable header is X-React-Router-Prerender-Data, a specific JSON object must be passed to it in order for the spoofing to be successful as we will see shortly. Here is the vulnerable code :
To use the header, React-router must be used in Framework mode, and for the attack to be possible the target page must use a loader.
Steps to reproduce
Versions used for our PoC:
"@react-router/node": "^7.5.0",
"@react-router/serve": "^7.5.0",
"react": "^19.0.0"
"react-dom": "^19.0.0"
"react-router": "^7.5.0"
Install React-Router with its default configuration in Framework mode (https://reactrouter.com/start/framework/installation)
Add a simple page using a loader (example: routes/ssr)
Access your page (which uses the loader) by suffixing it with .data. In our case the page is called /ssr:
We access it by adding the suffix .data and retrieve the data object, needed for the header:
Send your request by adding the X-React-Router-Prerender-Data header with the previously retrieved object as its value. You can change any value of your data object (do not touch the other values, the latter being necessary for the object to be processed correctly and not throw an error):
As you can see, all values have ...
April 24th, 2025 (8 days ago)
|
|
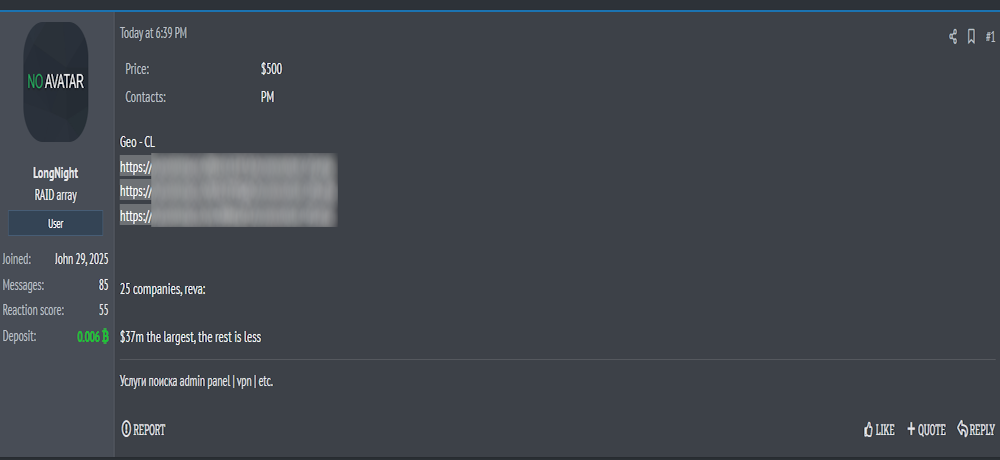
Description: Alleged Sale of Access to Multiple Unidentified Companies in Chile
April 24th, 2025 (8 days ago)
|
